For discussion, the original thread is available on Twitter.
1/ HOW DOES YOUR CRYPTO FUND OR EXCHANGE GETS HACKED
In the light of the recent event of a prop trading firm losing big monies in an old-fashioned Microsoft Word attachment attack, let me sip my tea and try to remember what kind of hacks I have seen over the years.
👇👇👇
In the light of the recent event of a prop trading firm losing big monies in an old-fashioned Microsoft Word attachment attack, let me sip my tea and try to remember what kind of hacks I have seen over the years.
👇👇👇
2/ I will skip all retail-focused attacks, like fake websites and weak passwords and only focus on serious cases where tanotable business pitself was a victim.
3/ Also no talk about SIM swapping etc. as it is the US only problem and only possible because the US does not have strong ids issued by the government (don't live in a crap nation plz.)
4/ Retail crime is a retail crime and not particularly interesting, as the cost of recovering assets would be higher than the asset value itself. So if you lost $5000 in a scam, please file a police report but you are not going to get money back.
5/ MICROSOFT WORD Attachment
Soon 50 years old MS Office codebase is full of old crappy C code ripe to blow up: macros, buffer overflows, etc.
Open a Microsoft Word document and you are almost guaranteed to have your computer trojaned with RAT (Remote Access Tool).
👇👇👇
Soon 50 years old MS Office codebase is full of old crappy C code ripe to blow up: macros, buffer overflows, etc.
Open a Microsoft Word document and you are almost guaranteed to have your computer trojaned with RAT (Remote Access Tool).
👇👇👇
8/ Case Bitstamp:
The sysadmin of Bitstamp got a GMail conversation where he was lied to receiving an honour (from some university / society). Then he was trojaned with a malicious Microsof Word document.
Bitstamp VPN to the server that has the exchange wallet had two-factor.
The sysadmin of Bitstamp got a GMail conversation where he was lied to receiving an honour (from some university / society). Then he was trojaned with a malicious Microsof Word document.
Bitstamp VPN to the server that has the exchange wallet had two-factor.
9/ However, this two-factor was disabled when VPN was run from the office.
10/ More Bitstamp incident details here:
The Bitstamp internal investigation post-mortem leaked and is full of good advise, but then it was wiped out from the Internet by Bitstamp legal team. github.com/miohtama/opsec…
The Bitstamp internal investigation post-mortem leaked and is full of good advise, but then it was wiped out from the Internet by Bitstamp legal team. github.com/miohtama/opsec…
11/ SOLUTION: Don't install Microsoft Office locally. Even better, don't use PCs and Microsoft products at all. Use Macs and online-only productivity suites (Google Workplace and Microsoft Office 365).
12/ SOCIAL HACKING AND SPOOFING
Also known as CEO fraud, Business Email Compromise (BEC) or Email Account Compromise (EAC)
👇👇👇
Also known as CEO fraud, Business Email Compromise (BEC) or Email Account Compromise (EAC)
👇👇👇
13/ This does not concern only crypto, but spoofing corporate invoices for Fortuna 500 companies is a good business. Wire transfers to wrong details and wrong reasons are common.
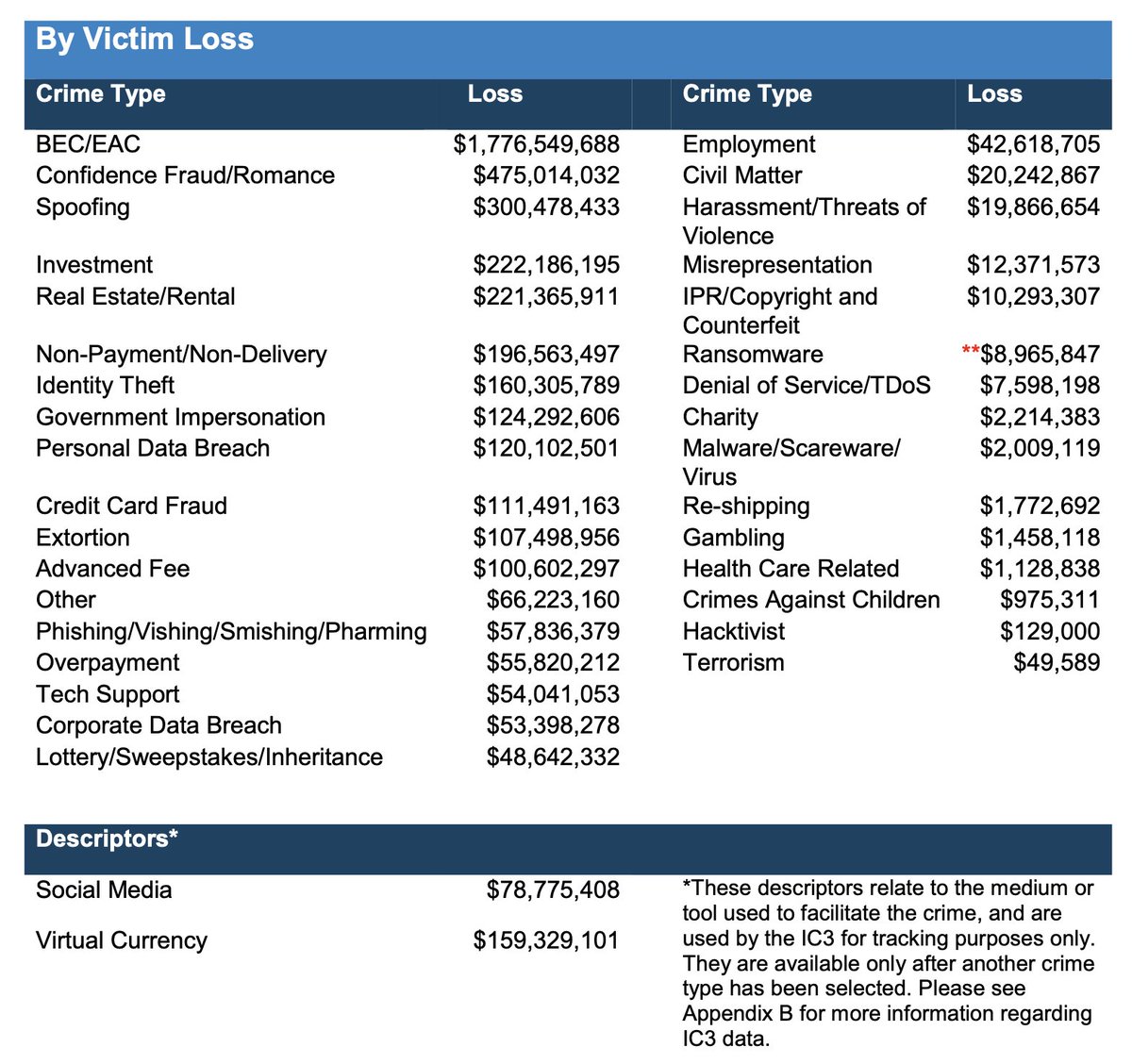 14/ CEO Fraud was in fact the most common form of fraud in the US. See the FBI cybercrime report 2019 (bear market, so the dynamics may have changed).
14/ CEO Fraud was in fact the most common form of fraud in the US. See the FBI cybercrime report 2019 (bear market, so the dynamics may have changed).
15/ Download the FBI report here ic3.gov/Media/PDF/Annu…
16/ Despite what the name says the email account password does not need to be compromised. in the CEO fraud, it is enough to pose as a CEO/CFO of a company and tell accountants to pay something somewhere very fast.
17/ Email sender spoofing is enough, as well as fake Slack account or social engineering by a call.
19/ SOLUTION:
Train your employees. Don't hire idiots. Don't be an idiot. Have four eyes on every operation so that a single person cannot agree on a high-value transaction alone (multisigs in the case of crypto.)
Train your employees. Don't hire idiots. Don't be an idiot. Have four eyes on every operation so that a single person cannot agree on a high-value transaction alone (multisigs in the case of crypto.)
20/ Then my favourite and most serious one:
COMPROMISING SERVER OR SERVICE PROVIDER
👇👇👇
COMPROMISING SERVER OR SERVICE PROVIDER
👇👇👇
21/ This could be either your server provider (likes of Amazon, Google, Hetzner) or more usually your DNS provider.
22/ FAMOUS VICTIMS: @gavinandresen
This early Bitcoin developer lost 46,000 bitcoins because of hosting a hot wallet on the @linode Virtual Private Server (VPS) provider.spectrum.ieee.org/thousands-of-b…
This early Bitcoin developer lost 46,000 bitcoins because of hosting a hot wallet on the @linode Virtual Private Server (VPS) provider.spectrum.ieee.org/thousands-of-b…
23/ In fact @linode has a history of losing all notable Bitcoin wallets ever hosted there. Internal support staff crime is rampant and uncontrolled.github.com/miohtama/opsec…
24/ The worst opsec email you can receive is a transactional email stating your server has a new network card installed, which you did not order.
25/ EtherDelta, an early DEX, was a victim of DNS hack. The attacker proxied the website and planted malicious elements to the web frontend. More here:bleepingcomputer.com/news/security/…
26/ SOLUTION: Don't use crappy server providers.
27/ Any server provider saying they are "privacy-oriented" and hosted in Switzerland usually means they are going to do internal fraud on high-value customers. A real story.
Stick with Amazon, Google, Hetzner, the other tier-one providers.
Stick with Amazon, Google, Hetzner, the other tier-one providers.
28/ Encrypt your hot wallet directories yourself and require a password on reboot.
29/ For DNS, don't use Godaddy, Namecheap, but use the same registrar that Google uses. Any retail DNS registrar is a joke.
I have personally reset the @Namecheap two-factor authentication by only using the information in emails they sent to me.
I have personally reset the @Namecheap two-factor authentication by only using the information in emails they sent to me.
30/ FIN
As a disclaimer, I advise crypto hedge funds on security. My merits include being at the receiving end of every possible cryptocurrency exchange attack (inc. all of those mentioned above) and losing eight figures of money in multisig wallet hack.
As a disclaimer, I advise crypto hedge funds on security. My merits include being at the receiving end of every possible cryptocurrency exchange attack (inc. all of those mentioned above) and losing eight figures of money in multisig wallet hack.
31/ The code is the only law the criminals honour.
32/ Now I am going to go to town to have some latte, as this tea makes me angry, and plan for my trip to Lisbon next week. See you there.
CC and greetings to @datarade and @Mudit__Gupta

Comments
Send any feedback and comments by replying the Twitter thread.
Discuss